For those not familar with Nomad from 1E: it is a peer to peer technology that helps elimintate Distribution Points with SCCM. The client will ask if any machine in the local Subnet has the files. If not it will then ask the ActiveEfficiency Server, assuming Single Site Download is setup, for files. 1E utilizes a Reverse QoS process along with many other cool features.
My enviroment has many types of machines that we want to consume data utilizing Nomad but not allow other machines to pull from it. For this 1E has a registry key. We have several instances of when you don't want to interrupt a machine. May it is a machine cluster crunching data, Video Editing machine, special server or maybe you have some political reasons as to exclude a machine.
The end result will be a machine with a Nomad Key
P2PElectionWeight set to 0
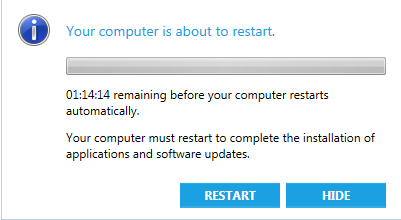
You must restart the Service for the machine to notice the change.
For this we create a Compliance check. There are several ways to create this:
Application
Find the MSI of the application you are detecting
At settings, click next
Select the approriate Platform
This is a quick Detection method, you can use anyone that works for you.
Here is a method I used to Detect if a machine has SQL install and Running:
(Note this example doesn't' include excluding SCCM Secondary servers)
First I wanted to find the machines that had SQL, this could also include SQL express and some machines with Bitlocker maybe seen as having SQL, which I found odd.
Now that we have a machine that has SQL detected we need to check to see if it is Running,
With both of these rules and more versions you can create detections if a machine has software installed. Remember if you have applications with the App Model then you have some work already done for you,
Now create your Baseline:
Software names have been removed from this list. Notice the purpose of these is "Prohibited" the reason is because we don't want these applications running.
The deployment is only run once a month before the patches as this is a heavy load on the enviroment. And we don't expect it to change much. This
To make this work we need a colleciton that has all the non-compliance machines
Create a package and push this Regfile to the machine to make it exempt from pulls
IF '%PROCESSOR_ARCHITEW6432%'=='' goto x86
reg.exe add HKLM\Software\1E\NomadBranch /v P2PElectionWeight /t REG_DWORD /d 0 /f /reg:64
:x86
reg.exe add HKLM\Software\1E\NomadBranch /v P2PElectionWeight /t REG_DWORD /d 0 /f
:: Restart the NomadBranch Service
NET STOP NomadBranch && NET START NomadBranch